Operata Cloud Collector Overview
What is Operata Cloud Collector?
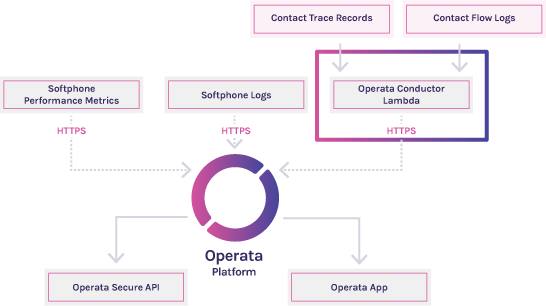
Operata Cloud Collector collects relevant contact and performance metadata for your Customers interactions within Amazon Connect and securely sends this data to the Operata Platform.
This data is correlated with both softphone performance metrics and other events collected for the lifecycle for the interaction.
This end-to-end view is presented inside the Operata UI with rich visualisations providing clear insights, powerful reporting, learning and alerting.
How Cloud Collector Works
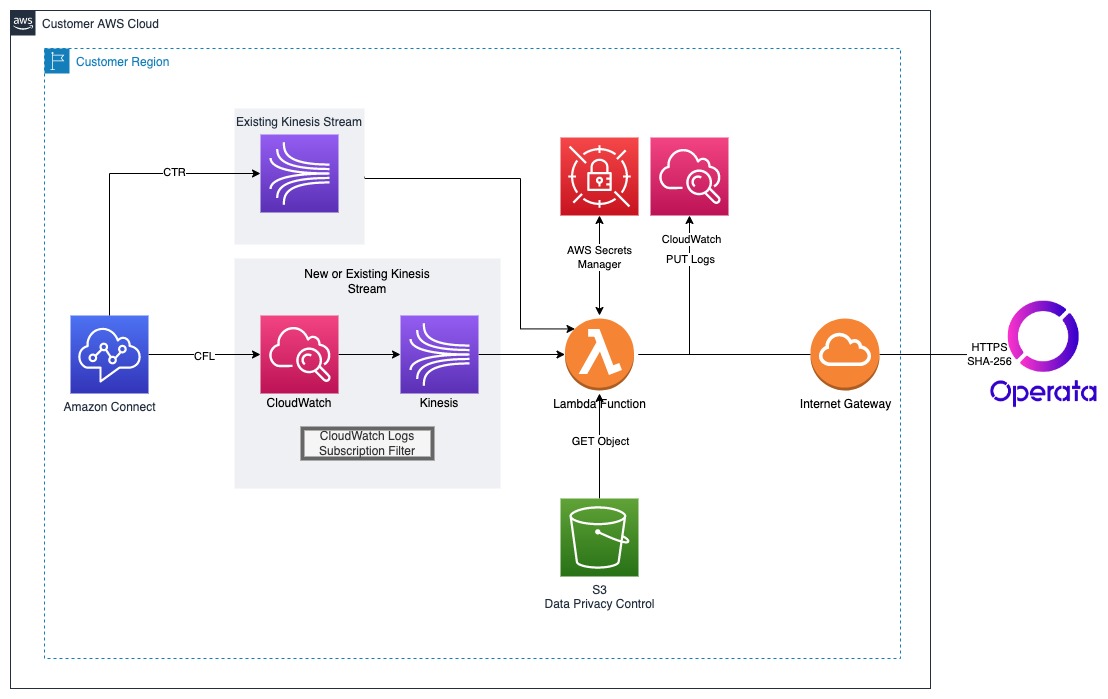
At the heart of Cloud Collector is a pre-built Lambda function provided by Operata which is implemented within your AWS instance using CloudFormation.
This Lambda function is fully configurable to ensure you are in total control of what data is sent to Operata.
Cloud Collector monitors your Amazon Connect instance for new or updated Contact Flow Logs (delivered to CloudWatch) and Contact Trace Records (delivered via Kinesis).
The data is securely shipped to the Operata platform via HTTPS, using SHA-256 with RSA Encryption.
Pre-Requisites
Before you begin, please ensure you have:
- An active Operata subscription: if you do not already have an active Operata subscription you can sign up for a free trial here
- Your Operata Group Credentials: if you do not already have your group credentials please contact us to have them generated.
- Approval from your Operata Customer Success Manager: if you do not already have permission to install please contact us.
Terms of ServiceBy installing Operata Software, you agree to and accept the Operata Terms Of Service
Skills required for deployment
This guide is intended for users familiar with AWS and the following services:
- CloudFormation
- Lambda
- Amazon Connect
- IAM
- Kinesis
Time to complete deployment
Allow 1 hour for deployment and testing of Operata Cloud Collector, comprised of:
- 0.5 hours for initial deployment
- 0.5 hours for testing
Deployment SchedulingDeployment of this service must be scheduled with Operata prior to deployment. Please contact your Customer Success Manager regarding scheduling.
Operata is not responsible for costs or damages caused by incorrect or unscheduled deployments.
Architecture Overview
Resources Deployed
The Operata CloudFormation template will deploy the following resources:
- Lambda Function
- Kinesis Stream (if not pre-existing)
- IAM Role & Policy
- CloudWatch log subscription filter
Deployment Options
This deployment type supports a single availability zone (AZ) only and is not designed for High Availability (HA). Should you require support for multi-AZ or multi-region please contact Operata support or your Customer Success Manager to discuss options.
Supported Regions
Operata supports all regions where Amazon Connect is available
IAM Roles & Policies Used by Cloud Collector
IAM PrivilegesOperata Cloud Collector uses a policy of least privilege for all access granted as part of the deployment.
Root PrivilegesWe strongly recommend that you do not use the root user for your everyday tasks, even the administrative ones. As a best practice, safeguard your root user credentials and don't use them for everyday tasks.
The following Roles & Policies will be created during deployment
| Role/Policy | Description |
|---|---|
| Lambda Execution | Allows the execution of the Lambda Function, Kinesis consumption & logging |
| Kinesis Creation | Allows the creation of a Kinesis Data Stream |
| CloudWatch Kinesis Subscription | Allows the Kinesis data stream to subscribe to CloudWatch a specified log group |
| S3 | Get Object |
Detailed Roles & Policies information can be found within the Operata CloudFormation templates
S3 Policies
There is no requirement for the Amazon S3 buckets to be deployed with policies allowing public access.
Secrets Management
An API key needs to be created within the Operata app and used when deploying Cloud Collector so that the Lambda function can securely send data to Operata.
Customer-sensitive data in the context of Cloud Collector relates to the API secret used in the service. Operata utilises AWS Secrets Manager to keep these secure. More information on AWS Secrets Manager and Operata Secret key rotation can be found below:
-
AWS Secrets Manager documentation can be found here
-
Operata Secret key rotation can be achieved within the Operata Console
Key Rotation
Key Rotation FrequencyOperata recommends a key rotation frequency of 90 days.
Steps to rotate keys:
- Log into Operata
- Go to Settings > Config > API
- Create a new key and copy the secret
- Log into AWS
- Go to Secrets Manager.
- Find your Secret labelled operata/
{GROUP_ID}/secret - Under Secret Value select Retrieve Secret Value
- Click Edit
- Paste your copied key secret from Step 3 and Save
- Return to Operata
- Select your old secret and choose delete
Data Encryption
Operata supports Data Encryption being enabled in Kinesis. For more information please see link to the AWS guides below. Please notify Operata support prior to deployment should you enable this service.
AWS Service Quotas
This deployment uses services that may impact the service quotas for your organisation. For more information on viewing your quotas or requesting increases please review the AWS service quotas guide
Billable AWS Services used in the deployment
Operata Cloud Collector uses the following services within your AWS Account. All usage is billable to the customers AWS account and is the responsibility of the customer to manage according to their own billing policies.
| Service | Quantity | Mandatory |
| Lambda | 1 Function | True |
| Kinesis | 1 Shard | True |
| S3 | 1 Object | False |
| AWS Secrets Manager | 1 Secret | True |
| AWS Secrets Manager | 1 API call per Lambda invocation | True |
Further information on usage cost estimation can be found here
Billable components
- Cloud Collector is included in all Operata plans. There are no additional costs billed by Operata to use this service.
- Amazon Connect
- Kinesis
- CloudWatch
Lambda Sizing
Cloud Collector is sized as per below:
| Memory Allocation | Timeout |
|---|---|
| 128MB | 20 seconds |
PerformanceOperata Cloud Collector has been suitably sized for most enterprise deployments, however, may need to be changed for some high-use circumstances. Please contact Operata support or your Customer Success Manager for further information.
Testing the deployment
- Customers will be assigned an Operata Engineer to test & certify the installation post-deployment.
- Logs are also available in the Lambda Console and/or CloudWatch to verify the installation.
Event DelaysEvents can take up to 5-minutes to appear within the Operata Console.
Troubleshooting the deployment
- Check for Lambda execution failures
- Confirm the correct credentials are being used against the correct
GroupId - Check Lambda Console and/or CloudWatch logs for information on failures
Please contact Operata support or your Customer Success Manager for further troubleshooting.
Monitoring Lambda
Logs and metrics are enabled by default. Lambda metrics and logs can be found in the Lambda Console and/or CloudWatch.
Viewing metrics In Lambda:
- Go to Lambda > Functions > Name of Lambda Function Deployed by CF Stack
- Choose Monitor > Metrics
- A good start to view the health of the Lambda is the Error count and success rate (%) metrics
Viewing logs In CloudWatch
- Go to CloudWatch > Logs > Log Groups > /aws/lambda/
{Name of Lambda Function Deployed by CF Stack} - Full DEBUG messages are available here to sort and filter.
- For more information on using filter patterns to match terms in log events see this AWS help guide
Updates and Patches
Should an update or patch be required to the Lambda function, Operata will contact your listed account administrator with instructions.
Failure Recovery
This service is not designed to be High Availability (HA). Should you have a requirement for HA or if you suffer a prolonged outage please contact Operata support or your Customer Success Manager to discuss options.
Other steps to recovery that can be attempted:
- Delete the CloudFormation stack.
- Re-deploy the CloudFormation stack.
- Monitor the CloudFormation output for errors.
Should an error be observed during stack creation contact Operata support or your Customer Success Manager for further support.
Updates
Operata will provide an updated CloudFormation template as part of updates or critical patches. Once you receive a notification from your Customer Success Manager or the Operata support team you can implement by following these steps:
- Login to AWS CloudFormation Console
- Find the previously created Operata stack
- Follow this AWS guide to delete the stack
- To install the update, follow the original instructions to deploy the Operata Lambda by following this guide
Outage Window RequiredPlease note: after deleting the CloudFormation stack your instance will not send Contact Trace Records or Contact Flow Logs until the new stack is installed. Please ensure this task is carried out during an appropriate window as per your business requirements.
Support
Business day support is available with all Operata plans. 24 x 7 Support is available on application.
| Channel | Details |
|---|---|
| Chat | In-app |
| [email protected] | |
| Phone | On Application |
Support SLA
Operata will use reasonable endeavors to provide an initial response to the Support Services requests promptly and in any event within the corresponding timeframe set out below:
| Severity Level | Underlying Issue | Initial Response Timeframe | Restoration Target |
|---|---|---|---|
| Critical | Inability to collect any Customer data | 2 Business Hours | 6 Business Hours |
| Serious | No access to the Operata platform or collected data | 4 Business Hours | 12 Business Hours |
| Moderate | Non-critical data or functionality issue | 8 Business Hours | 24 Business Hours |
| Minor | Any impairment of the Software not falling into the above categories; and any cosmetic issue affecting the Software | 16 Business Hours | 160 Business Hours |
Updated 9 months ago
